Why?
As OBIEE is targeted as an enterprise wide solution for reporting, and single point of truth, you might experience the need for securing your content based on your targeted audience.
This series of OBIEE Security posts will explain how this can be accomplished and a couple of base factors in implementing security.
You will have different categories of users seeing different content types. So, the first thing you’ll need to do is define these categories for your company/delivered solution.
Now, please note, a user is not restricted to a single category. For instance, you might have a category for High Management. The HR head of a company will pertain to this, but he can also pertain to a second HR group, looking only at HR related data.
However your user-group association is provided for OBIEE, either LDAP, Database table (maintained through an application), direct association in WebLogic, there are several steps you will still need to proceed with in setting up your security.
Please keep in mind all security is applied on Application Roles (as a best practice) – both content, privileges as well as data security. The following steps will guide you through the entire process of creating a user, the associated group, then the Application Role and setting up the membership setup for the above. This will help you further on in setting up you security.
How?
One of the biggest differences between OBIEE 10g security and OBIEE 11g security is that users and groups are no longer held primarily in the repository; instead, these details are held by default in the WebLogic Server LDAP server, which gets installed alongside OBIEE when you install the product.
Now, you create users and groups within this LDAP server, and administer these users and groups using the WebLogic Server Administration Console.
In an out-of-the box installation, the LDAP integration is not configured from start. So, if your list of users is not provided from outside, you will need to create them within WebLogic.
Creating a new user
For creating a new user, login to your WebLogic Server Administration Console with an admin user (e.g. weblogic), accessing the link formatted as ::/console.
By default, the server is defined as the IP address where you have installed your BI Instance, and the default port for the Administration Console is 7001.
Go to Security Realms on the left hand side of the screen:

then select the security realm your BI Server is using (Default is myrealm):

and navigate to Users and Groups -> Users:

In here, you will have a list of all existing users (both your regular application users as well as some internal administration users for OBIEE), and the possibility to modify, delete or add a user.
For creating the user, please make sure to fill in all appropriate details:


Groups
Groups are deprecated in OBIEE 11g, and are replaced by Application Roles in the setup of security.
However, you will notice they still appear in WebLogic Server Administration Console.
These are usually generated from LDAP (together with your users list and authentication method).
For creating a new group, please follow these steps:
– from my realm (previous step on creating new user) go to Groups from the Users and Groups tab

and add new group. Please make sure you fill in all appropriate details.
Group membership
Please note, a group does not have an automated allocated member / parent group.
For this, you will need to go to the list of groups, select your group and go to Membership

then select and drag on the right hand side the desired list of existing groups as a chosen parent group.

The above setup implies that the new group TopManagement is a member of BIConsumers. This is a generic group stating the user will be consuming/executing BI Content. I would recommend any new group to have this as a parent group.
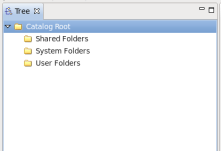
OBIEE Global Groups membership
On a new installation, you will notice 3 main groups that are created automatically by the system:
- BIConsumers
- BIAuthors
- BIAdministrators
The BIConsumers is the generic group of which all users are members. This defines a user as consuming OBIEE content (capable of executing reports and dashboards). Please note this implies only executing content.
BIAuthors group defines the list of users who can actually create and own content in OBIEE catalog. This content can be of various types, starting from saved customization, to analysis and dashboard content.
BIAdministrators defines the list of users who have administrative rights over the system: ownership, archive/unarchive content, privilege editing, security editing, e.t.c.
Now, there’s an implicit inclusion/membership logic for these groups.
Any BIAuthors user is automatically also a BIConsumers user, therefore, the BIAuthors membership has as parent group the BIConsumers one:

Also, in the same logic, any BIAdministrators user is also an author of content, therefore the BIAdministrators has as parent group BIAuthors:

User membership
Now, going back to our previous user, since his membership is not provided automatically through our LDAP configuration for this case, we will need to associate this user with the appropriate groups.
Go back to the Users and Groups -> Users and select your user from the users list

Edit your user

go to Groups tab, select your target group and drag it on the Chosen groups:

then save your changes:

Creating a new Application Role
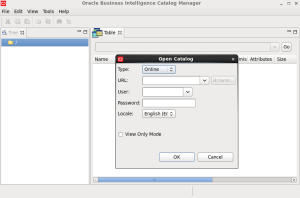
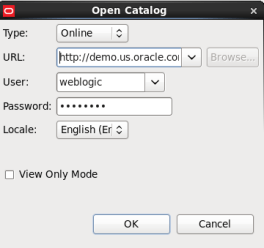
For creating a new Application Role, login to your WebLogic  Server Enterprise Manager with an admin user (e.g. weblogic), accessing the link formatted as ::/em.
Server Enterprise Manager with an admin user (e.g. weblogic), accessing the link formatted as ::/em.
By default, the server is defined as the IP address where you have installed your BI Instance, and the default port for the Administration Console is 7001.
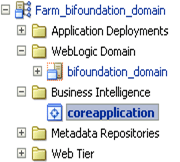
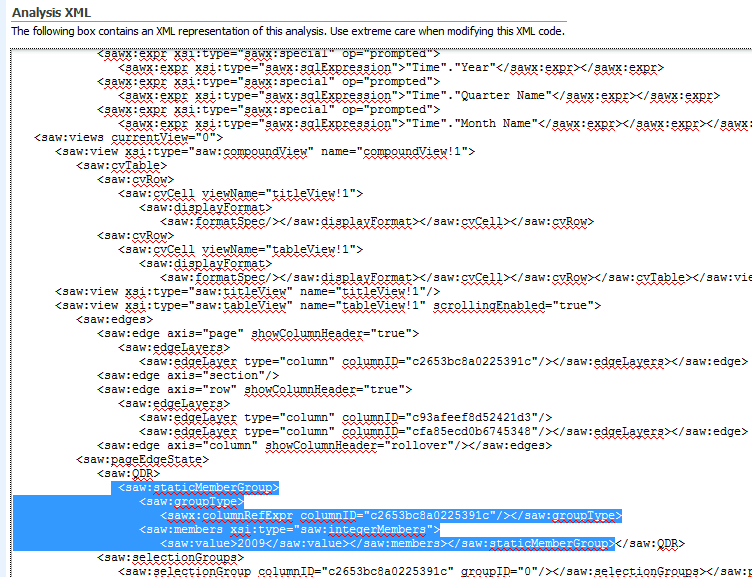
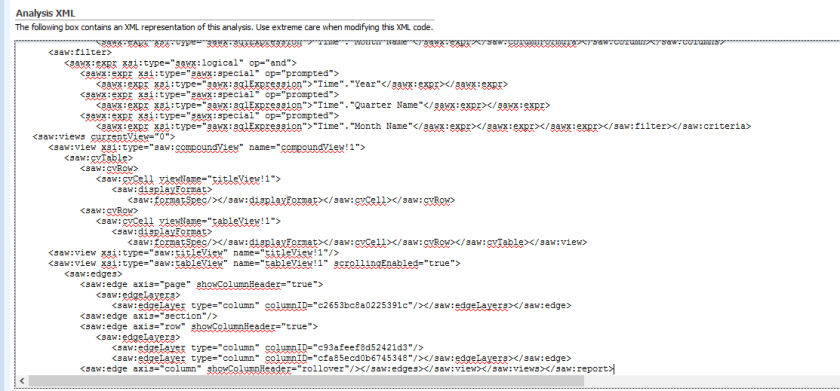
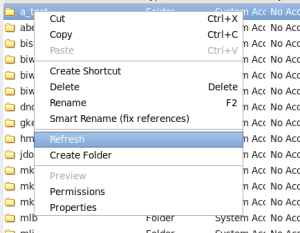
When the Enterprise Manager Homepage is displayed, navigate to the Business Intelligence > coreapplication menu item, then right-click on it. When the right-click menu is displayed, select Security > Application Roles (path might differ if you have a clustered BI Server).

The Application Roles page will then be displayed.

So at this point, there are three administrative tasks that you might need to perform around the WebLogic LDAP server, and application roles and policies:
- You may have to create new application roles, and assign users to these, either through existing LDAP groups or by creating some new ones
- You may have to alter or create new application policies, and
- You may need to bundle up these application roles and policies, and other security settings, and migrate these to a new server.
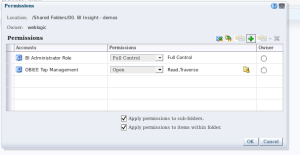
To create a new application Role, please make sure you specify all required criteria. Note that Display Name will be the name that will show up in Front-end/Presentation layer when you will want to apply security. If display name is null at creation time, display name will be the same as Role Name. Please make sure to fill in appropriate details in description field regarding the business scope of your role. This will be very helpful later on, when debugging and for other users.

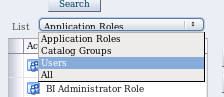
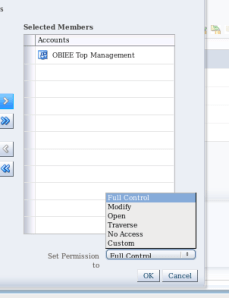
Another detail you should be mentioning when creating a role is the role Members. Usually, you will add in all groups that should pertain to this role, as well as any additional Roles, if required. You can also add individual users.

In our case, I have added for our application role the TopManagement group.
Search for desired the group and click on the arrow (if you want a full list just click on the arrow, as the initial display is empty).
 then make sure to select the desired group (it will become grayed out) before clicking ok:
then make sure to select the desired group (it will become grayed out) before clicking ok:

and then save your Application Role with all desired changes

this save will bring you back to the application roles list, with a success message on the top:

OBIEE Global Application Roles membership
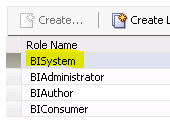
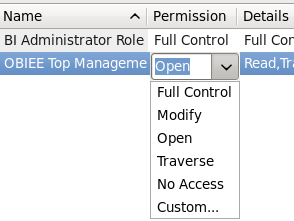
Please not the generic out-of-the box Application Roles that come with an OBIEE install:
- BIAutor
- BIConsumer
- BIAdministrator
Looking at membership, you will notice that BIAdministrator has as members ONLY the BIAdministrators group.

The BIAuhor has both BIAuthors associated group, as well as the BIConsumer Application role (the same type of inclusion we have noticed in the OBIEE groups)

while BIConsumer has BIConsumers associated group, as well as the BIAuthor Application role (the same type of inclusion we have noticed in the OBIEE groups) and a generic authenticated user application role (authenticated-role).

This last role is a generic OBIEE application role that any user who can login to your system will have by default.
Hope this helped you understand a bit of the logic behind users, groups and application roles.
Note: Please note this tests were done on OBIEE 11.1.1.7.1.







































 Server Enterprise Manager with an admin user (e.g. weblogic), accessing the link formatted as :
Server Enterprise Manager with an admin user (e.g. weblogic), accessing the link formatted as :