What?
You would have been into the situation where you were requested to apply security on the OBIEE exposed objects.
First level of security that we are going to discuss now is folder level security (this implies granting access to both folders as well as dashboards) through managing catalog security.
How?
There are 2 main options to implement this security:
- front end – from the presentation services
- back end – from the catalog manager
OBIEE Front-End Security
Browse through your catalog until you reach your desired main folder/object on which you want to apply security.
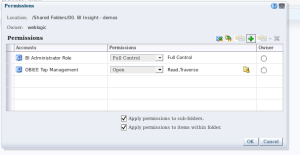
Our example shows application on the OBIEE folder “Shared Folders/00. BI Insight – demos”.
Select the folder from the tree at the right side and then click Permission from the bottom of the right column. Second option is selecting parent Folder from Tree view column, then select folder from list view column, and click on “More” link. A Permissions option/link will appear.
You will notice you have various options now available:
- Apply effective permissions
- Replace with parent’s folder permissions
- Set parent folders permissions to “Traverse Folder”
- Add users/roles
- Apply permissions for selected users/roles
- Delete selected users/roles
- Applying permissions to sub-folders (selecting a number of group/role/users – button will display the list of available privileges and apply the selection to all selection)
- Applying permissions to all items within folder
When adding permissions (on click on the plus button), you will have options to add Application Roles, Catalog Groups or Users. Search list allows you to select by any of the above categories, or overall: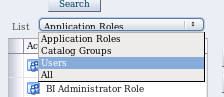
Write your search criteria (or leave blank when you want the full list) and click the Search button

then select the desired User/Role/Group and move to the right (Selected Members list):
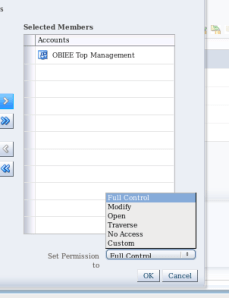
then select the type of Permissions you want to grant and click OK.
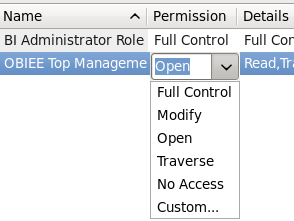
You can grant:
- Full Control

- Modify
- Open
- Traverse
- No Access
- Custom
- Custom permission allows any combination of the available rights on the right.
- Full Control – all rights from image;
- Modify – Read, Traverse, Write and Delete Permissions
- Open – Read & Traverse Rights (this is the typical right to be granted to a consumer of reports)
- Traverse – available only for folders – it allows users to access items within the folder, but not creating/adding additional information to the folder itself;
- No Access – denied access to the object
After getting your selections and rights in order, you can also set up the owner (by selecting the appropriate radio button – default is no selection if creator of report/current owner is not in the list). You can then apply your permissions on current folder only, or recursively on the sub-folders (child folder tree) and/or the items within the folder (analysis, dashboard, prompt, filter …) by checking the appropriate check-boxes at the bottom of the pop-up window:
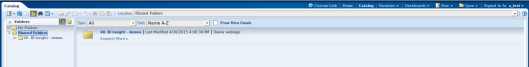
As a test, I’ve logged in with my test user a_test (member of OBIEE Top Management application role) and I can only see my selected folder in the Shared Reports folder.
OBIEE Back-End Security
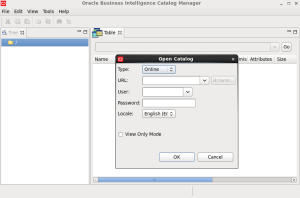
The second option of implementing this type of security is using the Catalog Manager tool.
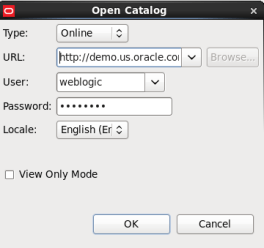
Open Catalog online, using Catalog manager
by specifying the URL and using an Admin user (e.g. weblogic)
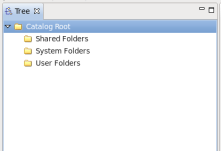
This will provide you with a Tree view
and a Table view:
You will be able to view:
- system folders
- shared folders
- users folders
All under root.
Please note the view provided by the catalog manager or namings will depend on your version of OBIEE. However, principles explained in this blog will still apply.
When selecting a given folder you can access various options, like Copy, Cut, Rename, Smart Rename, Create, Permissions and Properties.
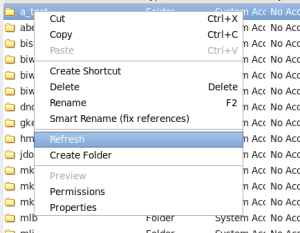
So Catalog manager will not only allow you to change permissions, but also properties (Applied recursively )

or managing your folders content.
The permissions screen is pretty much similar to the one on the OBIEE front end:
allowing adding permissions, changing them or removing them.
In the same way, you can add permissions on Application Roles and/or Catalog Groups and/or Users, with the same option types
You can apply changes Recursively, however this will apply them to both Sub-folders and items within the folder. There is no distinction at this level between the two types.
You also have a Replace Option, as presented bellow:

The effect on both security implementation options (Catalog Manager/Front End) is similar for the end user.
Applicability
There are various test cases when you might choose using the Catalog Manager over the Front-End setup of security.
One of the most common issues experienced by users is linked to the user’s personal folders:
- general unable to access (cannot see my folder)
- unable to access saved selections
- unable to create any more saved selection
In this type of scenario, Catalog Manger will allow you access to user’s folder. Solution is to re-grant the user Full Control to his own folder – applied recursively.
Note: Please note this tests were done on OBIEE 11.1.1.7.1.




This is good. But how do we apply Full Control to all users recursively in one go who are in ‘Additional users and groups list’ section when we open catalog offline. I have moved them them ‘Users and groups (Explicit Permissions)’ section but applying full control to all user folders in one go looks to be limitation for now. If you know a way please let know.
Hi Mohd,
I believe there is a simple solution to your puzzle.
You cannot select all users in the list of “Additional Users and Application Roles” to add them all with same right on a item in the catalog.
However, if the scope for your action is for you to grant access to any user who will login into your system to that object, the easiest way is to grant access on that object to a role encompassing all your users. One such role, is the BIConsumer role.
However, the one role who will grant any user who can login to your system access (any user who passes the login will have) is the “authenticateduser” Application Role.
Please try that one.
Please do comment if you found my answer useful.
Thanks,
Ioana
Thanks for your nice blog regarding OBIEE catalog permissions & privileges. I have a question to inquire: can we grant a developer to upload catalog reports to PRD without allowing them to do development work directly on that environment? In order to upload reports, the user has to be granted write permission, right? Many thanks.
Hi Joanne,
From what i have seen and tested so far there is no way to allow a user to do the archive-un-archive action on a BI server without him having the right to write on the server.
However, if the user does not have access to any Subject area, or other extensions (e.g. Answers access), the actions for creating might get limited to the migration alone.
Have not tested this but might try it during the next couple of days and come back with the confirmation.